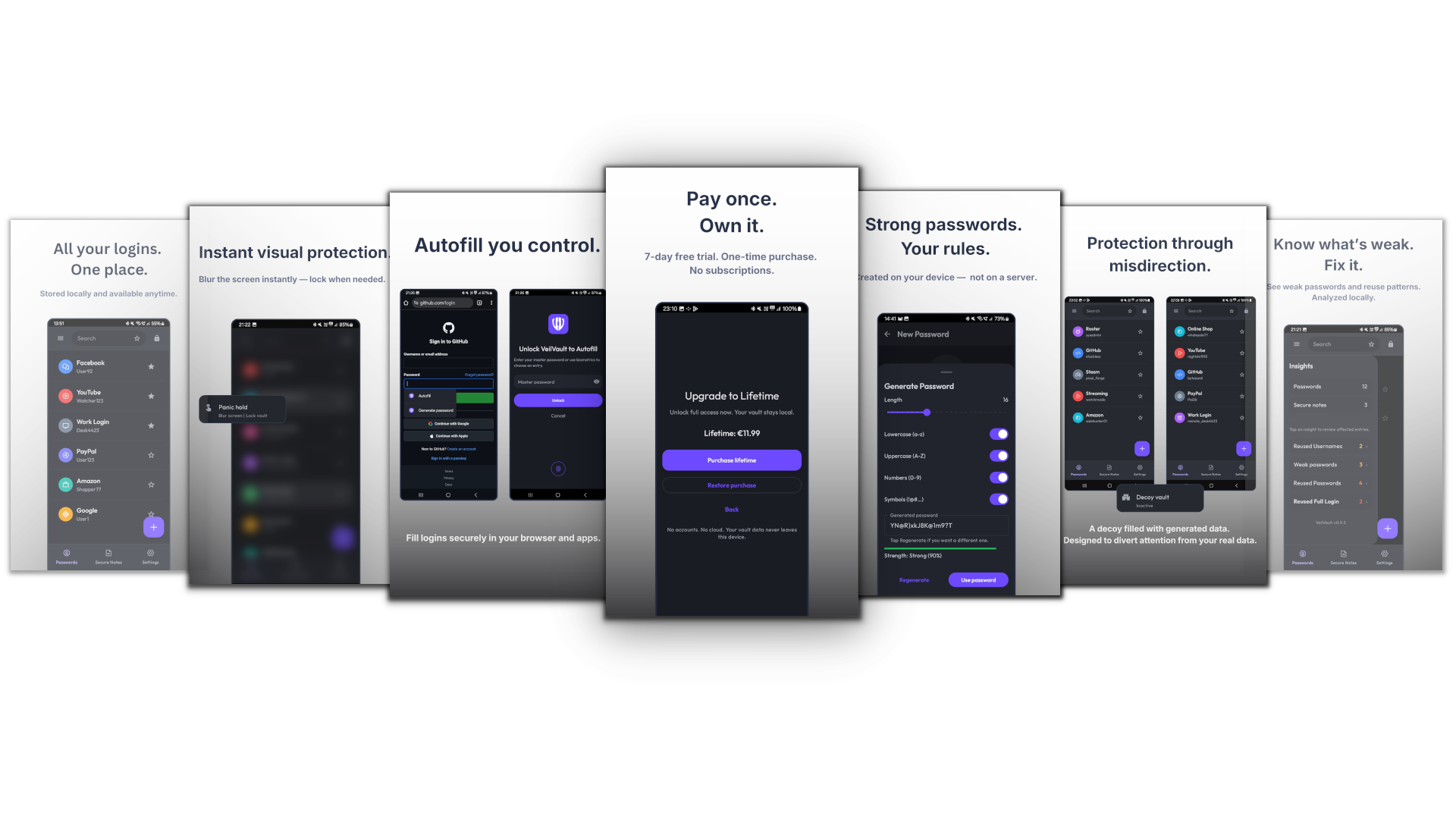
VeilVault
Local password vault for Android
VeilVault stores your credentials locally, encrypted on your device.
No accounts. No cloud dependency. No servers. Offline by design.
It exists for one reason:
to store secrets without expanding their exposure.